Between 2019 and December 2022, a particularly superior iMessage vulnerability was within the wild that was finally named “Operation Triangulation” by safety researchers at Kasperksy who found it. Now they’ve shared every thing they know in regards to the “most subtle assault chain” they’ve “ever seen.”
Immediately on the Chaos Communication Congress, Kaspersky safety researchers Boris Larin, Leonid Bezvershenko, and Georgy Kucherin gave a presentation masking Operation Triangulation. This marked the primary time the three “publicly disclosed the main points of all exploits and vulnerabilities that have been used” within the superior iMessage assault.
The researchers additionally shared all of their work on the Kaspersky SecureList blog immediately.
The Pegasus 0-click iMessage exploit has been known as “one of the technically subtle exploits.” And Operation Triangulation appears to be like to be at a equally scary degree – Larin, Bezvershenko, and Kucherin have stated “that is positively essentially the most subtle assault chain now we have ever seen.”
0-day assault chain to 0-click iMessage exploit
This vulnerability existed till iOS 16.2 was launched in December 2022.
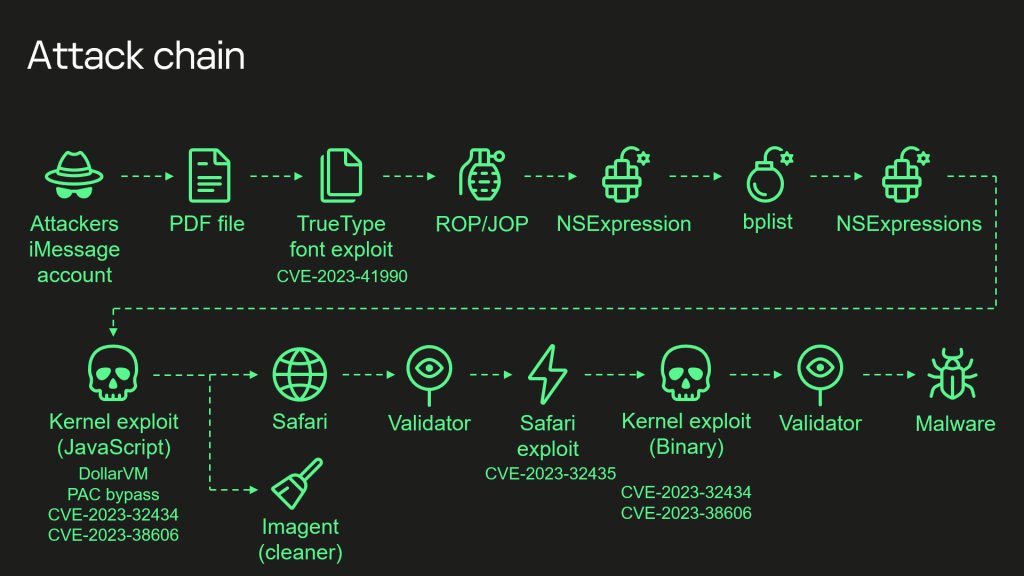
Right here’s the complete complicated assault chain together with the 4 0-days used to realize root privileges of a sufferer’s gadget:
- Attackers ship a malicious iMessage attachment, which the appliance processes with out displaying any indicators to the person.
- This attachment exploits the distant code execution vulnerability CVE-2023-41990 within the undocumented, Apple-only ADJUST TrueType font instruction. This instruction had existed for the reason that early nineties earlier than a patch eliminated it.
- It makes use of return/soar oriented programming and a number of phases written within the NSExpression/NSPredicate question language, patching the JavaScriptCore library setting to execute a privilege escalation exploit written in JavaScript.
- This JavaScript exploit is obfuscated to make it fully unreadable and to attenuate its dimension. Nonetheless, it has round 11,000 traces of code, that are primarily devoted to JavaScriptCore and kernel reminiscence parsing and manipulation.
- It exploits the JavaScriptCore debugging characteristic DollarVM ($vm) to realize the power to govern JavaScriptCore’s reminiscence from the script and execute native API capabilities.
- It was designed to help each previous and new iPhones and included a Pointer Authentication Code (PAC) bypass for exploitation of latest fashions.
- It makes use of the integer overflow vulnerability CVE-2023-32434 in XNU’s reminiscence mapping syscalls (mach_make_memory_entry and vm_map) to acquire learn/write entry to your complete bodily reminiscence of the gadget at person degree.
- It makes use of {hardware} memory-mapped I/O (MMIO) registers to bypass the Web page Safety Layer (PPL). This was mitigated as CVE-2023-38606.
- After exploiting all of the vulnerabilities, the JavaScript exploit can do no matter it needs to the gadget together with working spy ware, however the attackers selected to: (a) launch the IMAgent course of and inject a payload that clears the exploitation artefacts from the gadget; (b) run a Safari course of in invisible mode and ahead it to an online web page with the following stage.
- The net web page has a script that verifies the sufferer and, if the checks cross, receives the following stage: the Safari exploit.
- The Safari exploit makes use of CVE-2023-32435 to execute a shellcode.
- The shellcode executes one other kernel exploit within the type of a Mach object file. It makes use of the identical vulnerabilities: CVE-2023-32434 and CVE-2023-38606. Additionally it is large by way of dimension and performance, however fully totally different from the kernel exploit written in JavaScript. Sure elements associated to exploitation of the above-mentioned vulnerabilities are all that the 2 share. Nonetheless, most of its code can also be devoted to parsing and manipulation of the kernel reminiscence. It comprises numerous post-exploitation utilities, that are principally unused.
- The exploit obtains root privileges and proceeds to execute different phases, which load spy ware. We lined these phases in our earlier posts.
The researchers spotlight that they’ve nearly reverse-engineered “each facet of this assault chain” and can be publishing extra articles in 2024 going in-depth on every vulnerability and the way it was used.
However apparently, Larin, Bezvershenko, and Kucherin be aware there’s a thriller remaining in the case of CVE-2023-38606 they’d like assist with.
Particularly, it’s not clear how attackers would have recognized in regards to the hidden {hardware} characteristic:
We’re publishing the technical particulars, in order that different iOS safety researchers can verify our findings and provide you with potential explanations of how the attackers discovered about this {hardware} characteristic.
In conclusion, Larin, Bezvershenko, and Kucherin say that programs “that depend on ‘safety via obscurity’ can by no means be really safe.”
If you need to contribute to the mission, yow will discover the technical particulars on the Kaspersky post.
FTC: We use earnings incomes auto affiliate hyperlinks. More.

