Managed Gadget Attestation allows enterprises to confirm Apple units for safety, defending the company community. This is learn how to use it.
Safety background
In our interconnected world, the problem of gadget id performs a vital position in on-line safety. Conventional safety fashions use perimeter defenses plus a firewall to try to confirm units – and block malicious ones.
The thought behind perimeter defenses is {that a} community (or a part of a community) are secured in any respect the potential factors of entry into the community from the surface.
Perimeters will also be established through Digital Non-public Networks (VPNs) which solely permit exterior customers to attach by a single gadget or gateway (which is closely secured).
Perimeter defenses are designed to maintain exterior attackers at bay and out of inside networks. However within the trendy cell age, perimeter defenses now not serve a function as a result of units are cell and transfer from one location to a different.
Units at this time are smaller and could be hid. They are often introduced inside a corporation’s perimeter defenses effortlessly by guests and even by workers.
Resulting from these components, any try and confirm and observe a malicious cell gadget utilizing perimeter defenses is futile.
As an alternative, a Zero Belief safety mannequin is now used. The thought behind Zero Belief is each gadget or consumer is suspect till verified (“by no means belief, all the time confirm”).
One of many central tenets of Zero Belief is to interchange the perimeter mannequin with one among direct gadget to useful resource verification.
On this mannequin, every useful resource accessed on a community verifies the shopper gadget instantly – guaranteeing that the gadget is permitted to entry the useful resource. If a tool is not verified (or the consumer is not authenticated) entry is denied.
Moreover, the widespread use of cloud sources means many group sources are actually distributed and outdoors safety perimeters.
Exterior perimeter threats nonetheless exist equivalent to Direct Denial of Service (DDoS), Man-In-The-Center assaults, and ransomware – simply to call a couple of.
However most of these assault vectors are normally carried out by giant, gang, or state actors. As such they require a special safety mannequin.
Safety and managed units
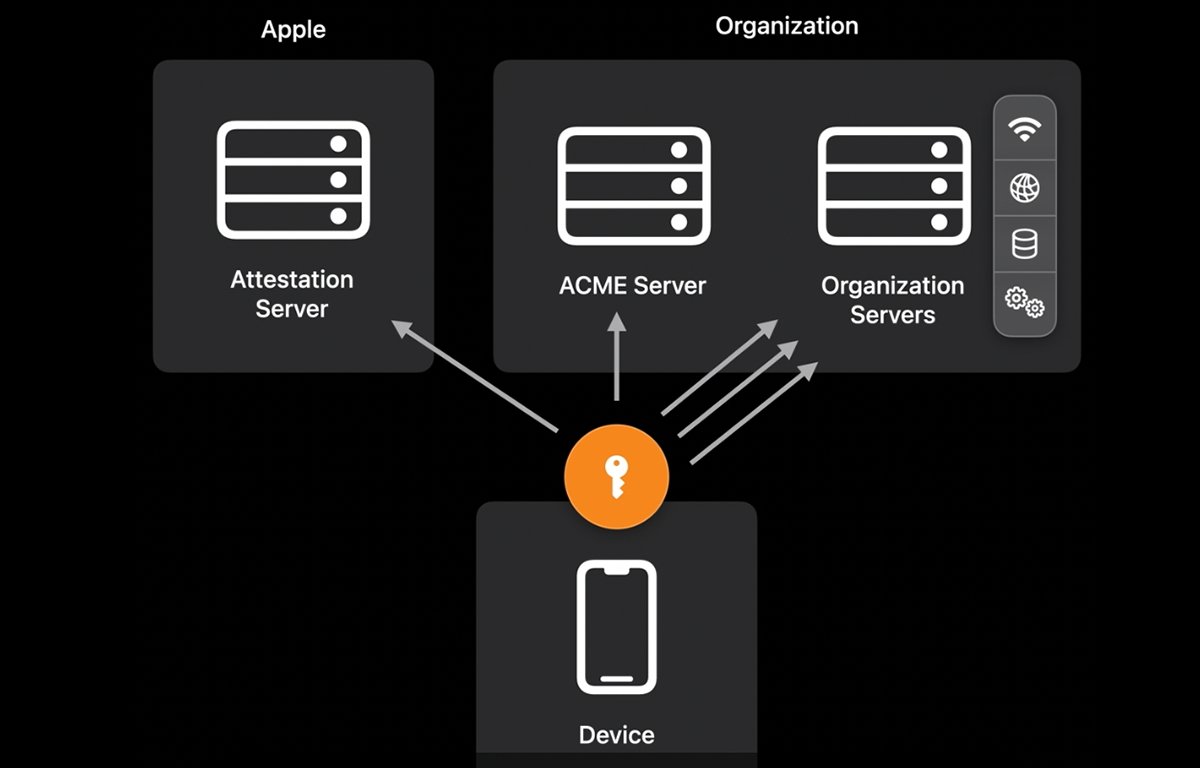
Apple solves the issue of safety on cell units utilizing a verification and belief scheme that includes a number of sources.
This contains an Apple gadget’s Safe Enclave – an space on newer Apple units that will comprise an Apple T2 chip, or a devoted safe space. Safe enclaves use {hardware} encryption and still have the flexibility to generate safe non-public keys tied to every gadget.
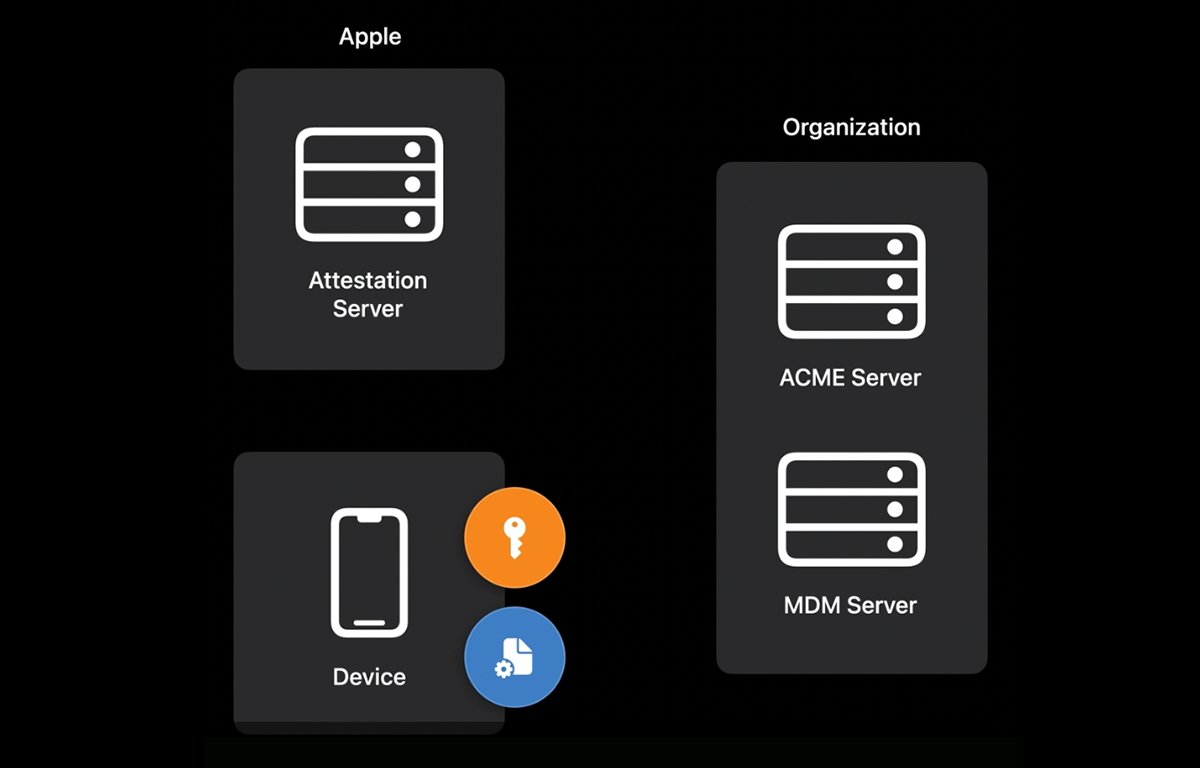
One other approach Apple and organizations safe units is through using Cell Gadget Administration (MDM) servers.
Computerized Certificates Administration Setting (ACME) servers will also be used – together with nonces (“Quantity-As soon as” or one-time safe random numbers), and encryption.
Internally Apple gives Gadget Attestation Servers (DAS), which comprise lists of all identified launched and bought Apple units, serial numbers, and gadget Safe Enclave particulars.
Apple DAS ensures Apple can confirm that any alleged Apple gadget attempting to speak with a community is the truth is, the gadget claimed.
Utilizing these elements in live performance, it is potential for a corporation or useful resource to confirm that an Apple gadget is genuine. This course of is named Managed Gadget Attestation (MDA).
MDA terminology
Safety is a posh matter so we won’t cowl each side of MDA right here. We’ll solely contact on a couple of key ideas.
However first, a bit terminology utilized in MDA and in laptop safety normally:
- Managed Gadget Attestation – the method of asserting and verifying an Apple gadget
- MDM Server – a server managed by a corporation or by Apple which manages Apple units
- Cryptographic key – a singular encoded quantity utilized in safe info alternate throughout a community
- PKI – Public Key Infrastructure – software program which manages cryptographic keys for safety functions
- ACME – The Computerized Certificates Administration Setting protocol used to automate the alternate of certificates info
- ACME server – a PKI certificates server managed by a corporation or by Apple which manages Apple units
- Nonce – in cryptography, a one-time distinctive (normally random) quantity used as an identifier in community communication
- Perimeter – and group’s or laptop’s encircling community safety inside which unauthorized communication will not be allowed
- Menace actor – a person or group which intends to hold out an assault on a community or on computing gadget(s)
- Assault floor – the methods during which a risk actor can break into or compromise a community or gadget
- Consumer – any distant laptop trying to hook up with a community, gadget, or laptop
- Belief analysis – the method of verifying a connecting gadget’s or consumer’s id
- Posture – in laptop safety a profile containing a number of items of details about a tool or consumer which helps in belief analysis
- UDID – a Distinctive Gadget quantity which identifies a tool
- Certificates – an encrypted file exchanged throughout a community to supply id and verification details about a tool – normally a server
- Attestation – a declaration of truth, which, as soon as verified permits a community to belief a tool or consumer
The ACME protocol makes use of JSON-formatted textual content over HTTPS and is outlined in IETF RFC 8555. ACME permits computer systems to automate the alternate of encrypted certificates to hurry up safe communication.
Apple’s servers and MDM servers talk with or use ACME servers within the Gadget Attestation course of.
In software program, an attestation is a truth that’s cryptographically signed. As soon as the signature is verified together with the gadget, the attestation is trusted. Utilizing a authorized analogy, consider an attestation as a verified, signed affidavit that states details.
Group servers can resolve how a lot gadget attestation they require with a view to belief a connecting gadget. Within the case of Apple units, attestations can embrace the gadget id, properties, and optionally, different information equivalent to certificates, profiles, and consumer IDs.
Utilizing Apple Gadget Attestation, an Apple gadget could be verified by receiving and trusting these details.
Gadget connection and verification
When an Apple gadget connects to a community, useful resource servers on the community can request gadget verification.
Throughout this course of, the connecting gadget is requested to hook up with any present MDM servers, which then triggers Apple’s Gadget Attestation Servers to confirm the gadget utilizing the gadget’s Safe Enclave.
Every trendy Apple gadget has its personal onboard Safe Enclave (which incorporates hardware-encrypted info). When the Safe Enclave verifies the gadget, Apple’s attestation servers ship a response to the MDM or group’s useful resource server to indicate the gadget is legitimate.
If verification fails, the gadget is denied entry to the requested group useful resource. Apple calls this gadget information the Belief Basis, which can embrace:
- Safe Enclave
- Apple attestation servers
- Manufacturing data (together with serial quantity)
- Working system catalog
MDM servers can difficulty a DeviceInformation command to an Apple gadget requesting the gadget information.
As soon as a tool’s attestation is returned to an MDM server, it is evaluated for validity. Gadget attestation declares to the MDM server that there’s, the truth is, a legitimate Apple gadget with the requested properties.
If ACME servers are used, an ACME payload will also be added. An ACME payload can be utilized in a tool’s ACME attestation, which additional helps confirm the gadget via a certificates.
ACME payloads help RSA or ECSECPrimeRandom encryption however it should be both 256-bit or 384-bit.
ACME is a bit just like the Easy Certificates Enrollment Protocol (SCEP) used on community gear. Most ACME server attestations require a hardware-bound key to make sure the knowledge being verified is tied to the particular connecting gadget.
If an ACME attestation is requested, an ACME server configures and points a brand new certificates, which the remainder of the group’s servers can belief.
Observe that the ACME attestation step normally solely occurs as soon as the bodily gadget attestation has accomplished. The certificates the ACME server points relies on a singular non permanent one-time non-public key generated by the Apple gadget itself.
There are extra methods the ACME payload could be verified, relying on how the gadget is connecting. These embrace Safari ID, Kerberos, Wi-Fi’s PayloadCertificateUUID, and a VPN’s PayloadCertificateUUID.
Every attestation can optionally use a singular nonce, or random quantity, throughout communication to make sure stale safety info cannot be used twice.
This ensures Man-In-The-Center assaults cannot happen which may impersonate a tool through a cast certificates.
If a malicious gadget tries to lie in regards to the Apple properties of a tool with a view to attempt to impersonate a tool, Apple’s attestation servers will reject it – and the gadget validation fails.
By utilizing a mix of those trusted particulars it turns into just about not possible to impersonate an Apple gadget. A number of attestations could be exchanged, resulting in an attestation chain.
Throughout gadget belief analysis, every server considers a tool’s and consumer’s safety Posture, or particulars, which may embrace:
- Consumer id
- Gadget id
- Location
- Connectivity
- Time
- Gadget administration
Fee limiting
Gadget attestation makes use of important sources on the gadget, together with energy. So Apple limits the variety of occasions and the frequency a tool attestation could be requested.
Typically, for DeviceInformation, Apple solely permits one request each seven days.
Utilizing a brand new nonce in an attestation signifies a brand new attestation is being requested, whereas omitting a nonce signifies the gadget’s earlier attestation can be utilized.
Apple defines a key for attestation nonces: DeviceAttestationNonce.
For these causes, servers or community units should not request a brand new attestation as quickly as potential. Somewhat solely request one when a tool property has modified, or if a sure time interval has elapsed.
Reacting to a failed attestation
Apple mentions that there isn’t any reliable solution to know why a tool attestation has failed, solely that it has.
Nevertheless, if a tool attestation does fail, the community or a server should not assume the worst – the failure could possibly be reliable and does not essentially point out an assault.
Further sources
The above description, is in fact a gross simplification. To grasp each element of Apple Gadget Attestation, remember to take a look at Apple’s WWDC ’22 session Discover Managed Device Attestation.
The attestation course of is definitely pretty complicated and takes some research to know totally.
For info on Apple PKI sources and certificates, see Apple PKI.
Utilizing Apple Managed Gadget Attestation, you’ll be able to vastly enhance the safety of your group’s Apple units in your community.
You’ll be able to confirm units earlier than permitting them to entry sources – and drastically cut back the chance a risk actor can use an Apple gadget as an assault vector.