AirDrop grew to become extremely popular in China lately, for the easy motive that the operate fully disguises the sender’s contact particulars. As AirDrop transmission doesn’t happen through the web or mobile phone community, however from iPhone to iPhone through Bluetooth identification and an area Wi-Fi community, it’s extraordinarily troublesome, if not unattainable, for authorities to determine senders. This allowed protesters to trade necessary messages, memes, and pictures with one another with out the police with the ability to crack the networks.
With the launch of iOS 16.1.1 round a yr in the past, nevertheless, Apple put in place a time limit of 10 minutes when sharing connections with Everybody, moderately than the default Contacts Solely setting. The official line was that this transfer was supposed to fight AirDrop spam and abuse, however the suspicion was that Apple was acceding to the desires of the Chinese language authorities–notably because the change utilized first in China.
Now a Chinese language state-licensed safety firm from Beijing claims (through Bloomberg) it has efficiently cracked the system and obtained the contact particulars of an AirDrop sender. The agency says its consultants have discovered log information for the AirDrop course of on a recipient’s iPhone; the machine identify of the sender’s iPhone, together with their e mail and phone quantity, is saved on the goal iPhone throughout information switch. Though the latter two particulars are transformed into hash values, the safety firm has discovered a way to transform these hash values into readable textual content.
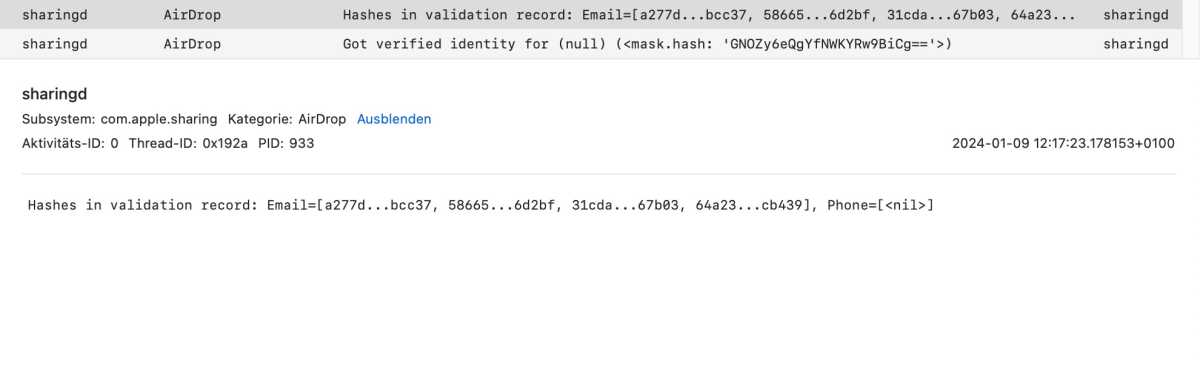
We will verify elements of this declare. We launched the console on our Mac and AirDropped a file to it from an iPhone, discovering from the console log information that the “sharingd” course of is chargeable for AirDrop. This comprises a devoted sub-process known as “AirDrop,” however a number of different sub-processes have been additionally lively through the file switch. We discovered the identify of our iPhone in one of many sub-processes, together with the power of the Bluetooth sign.
Gadget particulars within the console logs.
Halyna Kubiv
The “AirDrop” sub-process really shops the hash values for the e-mail and cellphone quantity belonging to the contacted iPhone (see screenshot), however we have been unable to entry the plain textual content.
Console logs through the AirDrop switch
.
Halyna Kubiv
Final however not least, it ought to be famous that our Mac and our iPhone are trusted gadgets, in any other case the AirDrop switch wouldn’t work in any respect. Even with unknown contacts, the recipient should first authorize the info switch; no international information are transferred with out their data. If the studies are true, AirDrop is a risk to dissidents in authoritarian states, as they consider they’ll stay nameless when exchanging information.
Why didn’t Apple repair the flaw?
Safety researchers have been warning Apple since no less than 2019 that the AirDrop protocol is flawed and will be cracked. In August 2021, the group led by Alexander Heinrich at TU Darmstadt introduced a way more safe various called Private Drop.
The issue with AirDrop is that the protocol requests the handle and cellphone quantity verified through the Apple ID from the sender’s machine and the recipient’s machine when establishing a connection if these should not within the handle guide of each events. Though they’re saved as hash values, they’re pretty straightforward to decipher: the cellphone quantity consists solely of digits and is simple to decode utilizing a brute-force assault. For emails, attackers guess the standard alias buildings, then seek for potential matches in dictionaries and databases of leaked emails.
In response to Heinrich, it was solely a matter of time earlier than the safety gaps in AirDrop have been abused. Nevertheless, the researchers have up to now solely intercepted the info throughout transmission makes an attempt. The truth that the non-public information of AirDrop contacts is saved domestically on the iPhone was beforehand unknown.
Heinrich says Apple reportedly contacted the researchers from Darmstadt concerning the loophole manner again when iOS 16 was nonetheless in improvement. Nevertheless, Heinrich was unable to search out any vital modifications to the switch protocol safety. Apple’s problem could be that the newer and safer model of the AirDrop protocol wouldn’t be backward appropriate with older iOS variations, he added.
This text initially appeared on Macwelt and was translated and edited by David Worth.

